
- Email support@dumps4free.com

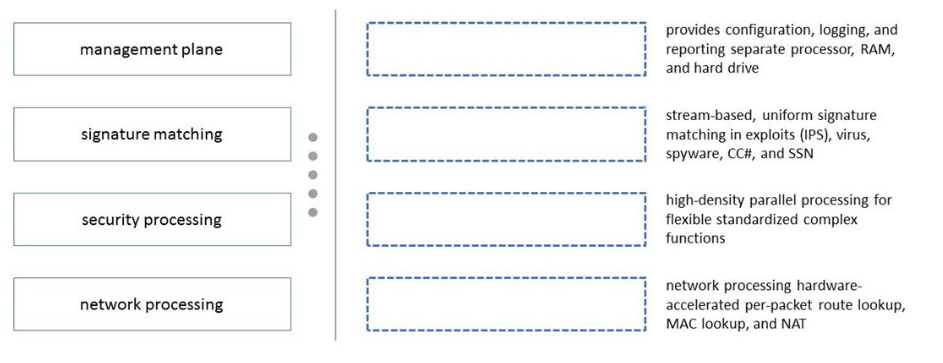
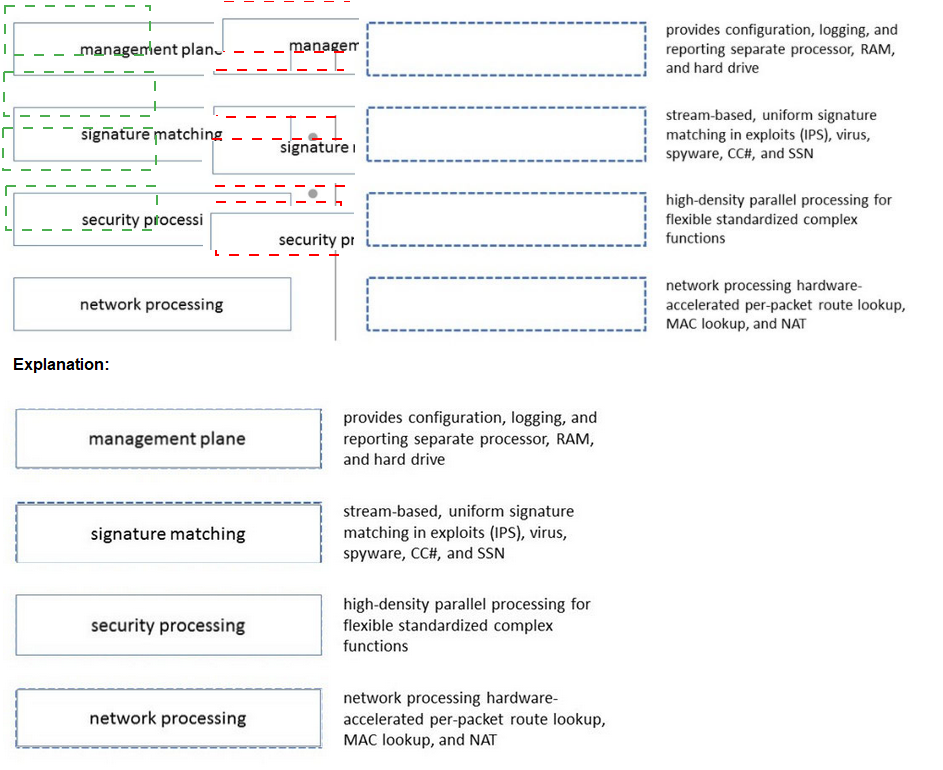
Please match the terms to their corresponding definitions.
An administrator has a Palo Alto Networks NGFW. All security subscriptions and decryption are enabled and the system is running close to its resource limits. Knowing that using decryption can be resource-intensive, how can the administrator reduce the load on the firewall?
A. Use RSA instead of ECDSA for traffic that isn't sensitive or high-priority.
B. Use the highest TLS protocol version to maximize security.
C. Use ECDSA instead of RSA for traffic that isn't sensitive or high-priority.
D. Use SSL Forward Proxy instead of SSL Inbound Inspection for decryption.
Explanation: Decryption can be resource-intensive, and in scenarios where the firewall is
nearing its resource limits, optimizing decryption practices is crucial. One way to do this is
by choosing more efficient encryption algorithms that require less computational power.
C. Use ECDSA instead of RSA for traffic that isn't sensitive or high-priority:
Elliptic Curve Digital Signature Algorithm (ECDSA) is known for requiring smaller
key sizes compared to RSA for a comparable level of security. This translates to
less computational overhead during the encryption and decryption processes.
By using ECDSA for traffic that isn't sensitive or high-priority, the administrator can
reduce the processing load associated with decryption on the firewall. This is
particularly beneficial in scenarios where resource optimization is necessary.
It's important to note that this approach does not compromise the security of
encrypted traffic. Instead, it offers a more resource-efficient way to manage
decryption, thus helping to maintain firewall performance even when system
resources are under significant demand.
By judiciously applying this strategy, administrators can manage the decryption workload
on the firewall, ensuring continued protection and inspection of encrypted traffic without
overburdening the firewall's resources.
Which Panorama mode should be used so that all logs are sent to. and only stored in. Cortex Data Lake?
A. Log Collector
B. Panorama
C. Legacy
D. Management Only
An engineer is troubleshooting a traffic-routing issue. What is the correct packet-flow sequence?
A. PBF > Zone Protection Profiles > Packet Buffer Protection
B. BGP > PBF > NAT
C. PBF > Static route > Security policy enforcement
D. NAT > Security policy enforcement > OSPF
Explanation: The correct packet-flow sequence is C. PBF > Static route > Security policy enforcement. This sequence describes the order of operations that the firewall performs when processing a packet. PBF stands for Policy-Based Forwarding, which is a feature that allows the firewall to override the routing table and forward traffic based on the source and destination addresses, application, user, or service. PBF is evaluated before the static route lookup, which is the default method of forwarding traffic based on the destination address and the longest prefix match. Security policy enforcement is the stage where the firewall applies the security policy rules to allow or block traffic based on various criteria, such as zone, address, port, user, application, etc.
Which two profiles should be configured when sharing tags from threat logs with a remote User-ID agent? (Choose two.)
A. Log Ingestion
B. HTTP
C. Log Forwarding
D. LDAP
Explanation: >Threat logs, create a log forwarding profile to define how you want the firewall or Panorama to handle logs. >Configure an HTTP server profile to forward logs to a remote User-ID agent. > Select the log forwarding profile you created then select this server profile as the HTTP server profile https://docs.paloaltonetworks.com/pan-os/11- 0/pan-os-admin/policy/use-auto-tagging-to-automate-security-actions
| Page 5 out of 59 Pages |
| Previous |