
- Email support@dumps4free.com

Refer to the exhibit.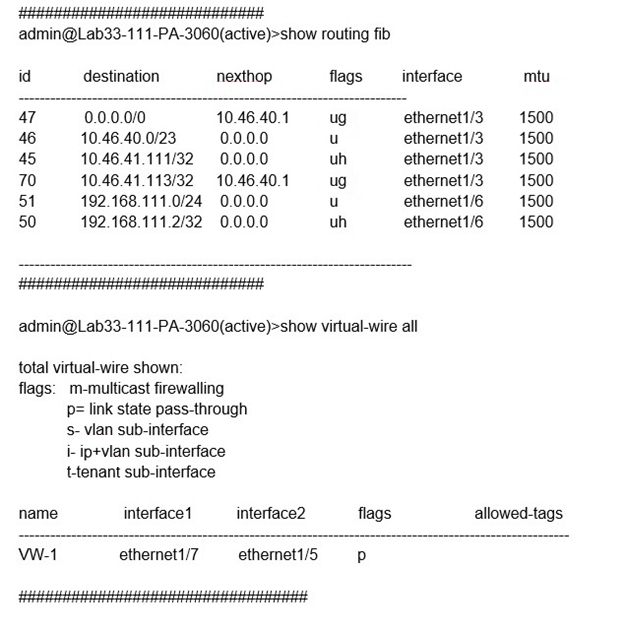
Which will be the egress interface if the traffic's ingress interface is ethernet1/7 sourcing
from 192.168.111.3 and to the destination 10.46.41.113?
A. ethernet1/6
B. ethernet1/3
C. ethernet1/7
D. ethernet1/5
Explanation: In the second image, VW ports mentioned are 1/5 and 1/7. Hence it can not be a part of any other routing. So if any traffic coming as ingress from 1/7, it has to go out via 1/5. The egress interface for the traffic with ingress interface ethernet1/7, source 192.168.111.3, and destination 10.46.41.113 will be ethernet1/5. This is because the traffic will match the virtual wire with interfaces ethernet1/5 and ethernet1/7, which is configured to allow VLAN-tagged traffic with tags 10 and 201. The traffic will also match the security policy rule that allows traffic from zone Trust to zone Untrust, which are assigned to ethernet1/7 and ethernet1/5 respectively2. Therefore, the traffic will be forwarded to the same interface from which it was received, which is ethernet1/53.
A firewall administrator wants to be able at to see all NAT sessions that are going ‘through a firewall with source NAT. Which CLI command can the administrator use?
A. show session all filter nat-rule-source
B. show running nat-rule-ippool rule "rule_name
C. show running nat-policy
D. show session all filter nat source
A superuser is tasked with creating administrator accounts for three contractors. For compliance purposes, all three contractors will be working with different device-groups in their hierarchy to deploy policies and objects. Which type of role-based access is most appropriate for this project?
A. Create a Dynamic Read only superuser
B. Create a Dynamic Admin with the Panorama Administrator role
C. Create a Device Group and Template Admin
D. Create a Custom Panorama Admin
Explanation: Custom Panorama Admin: Custom Panorama Admin roles allow you to customize the elements of Panorama that an administrator can access. You can hide tabs in the web interface, you can set specific items in Panorama to read-only, or you can limit an administrator’s access to Panorama plugins. Custom Panorama Admin roles require planning and configuration, but they provide extensive flexibility because you can control what administrators can access through the web interface or the CLI. Device Group and Template Admin: Device Group and Template Admin roles also require configuration because there are no built-in examples. These Admin Roles allow you to define which Panorama templates or Panorama device groups an administrator can access and configure. You can hide tabs in the web interface or set specific items to read only to control what administrators can configure.
What would allow a network security administrator to authenticate and identify a user with a new BYOD-type device that is not joined to the corporate domain?
A. an Authentication policy with 'unknown' selected in the Source User field
B. an Authentication policy with 'known-user' selected in the Source User field
C. a Security policy with 'known-user' selected in the Source User field
D. a Security policy with 'unknown' selected in the Source User field
Explanation: For a network security administrator to authenticate and identify a user with a
new BYOD-type device that is not joined to the corporate domain, the most effective
method is to use an Authentication policy targeting users not yet identified by the system.
A. an Authentication policy with 'unknown' selected in the Source User field:
An Authentication policy allows the firewall to challenge unidentified users for
credentials. By selecting 'unknown' in the Source User field, the policy targets
users who have not yet been identified by the firewall, which would include users
on new BYOD devices not joined to the domain.
Once the user provides valid credentials, the firewall can authenticate the user and
map their identity to subsequent sessions, enabling the application of user-based
policy rules and monitoring.
This approach ensures that new and unknown devices can be properly authenticated and
identified without compromising security or requiring the device to be part of the corporate
domain.
Which GloDalProtecI gateway setting is required to enable split-tunneting by access route, destination domain and application?
A. Tunnel mode
B. Satellite mode
C. IPSec mode
D. No Direct Access to local networks
| Page 4 out of 59 Pages |
| Previous |