
- Email support@dumps4free.com

An important patch for a critical application has just been released, and a systems administrator is identifying all of the systems requiring the patch. Which of the following must be maintained in order to ensure that all systems requiring the patch are updated?
A. Asset inventory
B. Network enumeration
C. Data certification
D. Procurement process
Explanation: To ensure that all systems requiring the patch are updated, the systems administrator must maintain an accurate asset inventory. This inventory lists all hardware and software assets within the organization, allowing the administrator to identify which systems are affected by the patch and ensuring that none are missed during the update process. Network enumeration is used to discover devices on a network but doesn't track software that requires patching. Data certification and procurement process are unrelated to tracking systems for patching purposes.
An employee recently resigned from a company. The employee was responsible for managing and supporting weekly batch jobs over the past five years. A few weeks after the employee resigned. one of the batch jobs talked and caused a major disruption. Which of the following would work best to prevent this type of incident from reoccurring?
A. Job rotation
B. Retention
C. Outsourcing
D. Separation of duties
Explanation: Job rotation is a security control that involves regularly moving employees to different roles within an organization. This practice helps prevent incidents where a single employee has too much control or knowledge about a specific job function, reducing the risk of disruption when an employee leaves. It also helps in identifying any hidden issues or undocumented processes that could cause problems after an employee's departure. References: CompTIA Security+ SY0-701 Course Content: Domain 5: Security Program Management and Oversight, which includes job rotation as a method to ensure business continuity and reduce risks.
Which of the following describes the maximum allowance of accepted risk?
A. Risk indicator
B. Risk level
C. Risk score
D. Risk threshold
Explanation: Risk threshold is the maximum amount of risk that an organization is willing to accept for a given activity or decision. It is also known as risk appetite or risk tolerance. Risk threshold helps an organization to prioritize and allocate resources for risk management. Risk indicator, risk level, and risk score are different ways of measuring or expressing the likelihood and impact of a risk, but they do not describe the maximum allowance of accepted risk. References: CompTIA Security+ Study Guide: Exam SY0-701, 9th Edition, page 34; Accepting Risk: Definition, How It Works, and Alternatives
Which of the following security controls is most likely being used when a critical legacy server is segmented into a private network?
A. Deterrent
B. Corrective
C. Compensating
D. Preventive
Explanation: When a critical legacy server is segmented into a private network, the security control being used is compensating. Compensating controls are alternative measures put in place to satisfy a security requirement when the primary control is not feasible or practical. In this case, segmenting the legacy server into a private network
serves as a compensating control to protect it from potential vulnerabilities that cannot be mitigated directly.
Compensating: Provides an alternative method to achieve the desired security outcome when the primary control is not possible.
Deterrent: Aims to discourage potential attackers but does not directly address segmentation.
Corrective: Used to correct or mitigate the impact of an incident after it has occurred.
Preventive: Aims to prevent security incidents but is not specific to the context of segmentation.
Reference: CompTIA Security+ SY0-701 Exam Objectives, Domain 1.1 - Compare and contrast various types of security controls (Compensating controls).
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal. The following is the audit report:
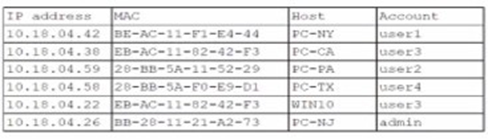
Which of the following is the most likely way a rogue device was allowed to connect?
A. A user performed a MAC cloning attack with a personal device.
B. A DMCP failure caused an incorrect IP address to be distributed
C. An administrator bypassed the security controls for testing.
D. DNS hijacking let an attacker intercept the captive portal traffic.
Explanation: The most likely way a rogue device was able to connect to the network is through a MAC cloning attack. In this attack, a personal device copies the MAC address of an authorized device, bypassing the 802.1X access control that relies on known hardware addresses for network access. The matching MAC addresses in the audit report suggest that this technique was used to gain unauthorized network access.
References = CompTIA Security+ SY0-701 Course Content: Domain 03 Security Architecture. CompTIA Security+ SY0-601 Study Guide: Chapter on Network Security and MAC Address Spoofing.
| Page 14 out of 78 Pages |
| Previous |