
- Email support@dumps4free.com

You have a network with ArubaOS-Switches for which Aruba ClearPass Policy Manager
(CPPM) is acting as a TACACS+ server to authenticate managers. CPPM assigns the
admins a TACACS+ privilege level, either manager or operator. You are now adding
ArubaOS-CX switches to the network. ClearPass admins want to use the same CPPM
service and policies to authenticate managers on the new switches.
What should you explain?
A. This approach cannot work because the ArubaOS-CX switches do not accept standard TACACS+ privilege levels.
B. This approach cannot work because the ArubaOS-CX switches do not support TACACS+.
C. This approach will work, but will need to be adjusted later if you want to assign managers to the default auditors group.
D. This approach will work to assign admins to the default "administrators" group, but not to the default "operators" group.
Explanation: With ArubaOS-CX switches, the use of ClearPass Policy Manager (CPPM) as a TACACS+ server for authentication is supported. The privilege levels assigned by CPPM will translate onto the switches, where the "manager" privilege level typically maps to administrative capabilities and the "operator" privilege level maps to more limited capabilities. ArubaOS-CX does support standard TACACS+ privilege levels, so administrators can be assigned appropriately. If the ClearPass policies are correctly configured, they will work for both ArubaOS-Switches and ArubaOS-CX switches. The distinction between the "administrators" and "operators" groups is inherent in the ArubaOSCX role-based access control, and these default groups need to be appropriately mapped to the TACACS+ privilege levels assigned by CPPM.
You are troubleshooting an authentication issue for Aruba switches that enforce 802 IX10 a
cluster of Aruba ClearPass Policy Manager (CPPMs) You know that CPPM Is receiving
and processing the authentication requests because the Aruba switches are showing
Access-Rejects in their statistics However, you cannot find the record tor the Access-
Rejects in CPPM Access Tracker
What is something you can do to look for the records?
A. Make sure that CPPM cluster settings are configured to show Access-Rejects
B. Verify that you are logged in to the CPPM Ul with read-write, not read-only, access
C. Click Edit in Access viewer and make sure that the correct servers are selected.
D. Go to the CPPM Event Viewer, because this is where RADIUS Access Rejects are stored.
Explanation: If Access-Reject records are not showing up in the CPPM Access Tracker, one action you can take is to ensure that the CPPM cluster settings are configured to display Access-Rejects. Cluster-wide settings in CPPM can affect which records are visible in Access Tracker. Ensuring that these settings are correctly configured will allow you to view all relevant authentication records, including Access-Rejects.
Refer to the exhibit.
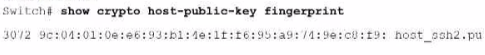
How can you use the thumbprint?
A. Install this thumbprint on management stations to use as two-factor authentication along with manager usernames and passwords, this will ensure managers connect from valid stations
B. Copy the thumbprint to other Aruba switches to establish a consistent SSH Key for all switches this will enable managers to connect to the switches securely with less effort
C. When you first connect to the switch with SSH from a management station, make sure that the thumbprint matches to ensure that a man-in-t he-mid die (MITM) attack is not occurring
D. install this thumbprint on management stations the stations can then authenticate with the thumbprint instead of admins having to enter usernames and passwords.
Explanation: The thumbprint (also known as a fingerprint) of a certificate or SSH key is a hash that uniquely represents the public key contained within. When you first connect to the switch with SSH from a management station, you should ensure that the thumbprint matches what you expect. This is a security measure to confirm the identity of the device you are connecting to and to ensure that a man-in-the-middle (MITM) attack is not occurring. If the thumbprint matches the known good thumbprint of the switch, it is safe to proceed with the connection.
How can hackers implement a man-in-the-middle (MITM) attack against a wireless client?
A. The hacker uses a combination of software and hardware to jam the RF band and prevent the client from connecting to any wireless networks.
B. The hacker runs an NMap scan on the wireless client to find its MAC and IP address. The hacker then connects to another network and spoofs those addresses.
C. The hacker connects a device to the same wireless network as the client and responds to the client’s ARP requests with the hacker device’s MAC address.
D. The hacker uses spear-phishing to probe for the IP addresses that the client is attempting to reach. The hacker device then spoofs those IP addresses.
Explanation: A common method for hackers to perform a man-in-the-middle (MITM) attack
on a wireless network is by ARP poisoning. The attacker connects to the same network as
the victim and sends false ARP messages over the network. This causes the victim's
device to send traffic to the attacker's machine instead of the legitimate destination,
allowing the attacker to intercept the traffic.
Reference: ARP spoofing is documented as a common MITM technique in various security
publications and resources like the IEEE 802.11 standard and security textbooks.
Please note that the answers provided are based on general networking and security
principles and best practices. If you require verification against specific Aruba product
documentation or technical manuals, those documents should be consulted directly.
Refer to the exhibit.
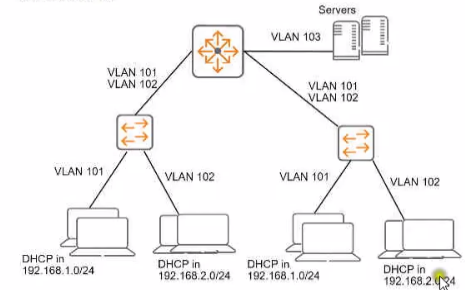
You need to ensure that only management stations in subnet 192.168.1.0/24 can access
the ArubaOS-Switches' CLI. Web Ul. and REST interfaces The company also wants to let
managers use these stations to access other parts of the network What should you do?
A. Establish a Control Plane Policing class that selects traffic from 192.168 1.0/24.
B. Specify 192.168.1.0.255.255.255.0 as authorized IP manager address
C. Configure the switch to listen for these protocols on OOBM only.
D. Specify vlan 100 as the management vlan for the switches.
Explanation: To ensure that only management stations in the subnet 192.168.1.0/24 can access the ArubaOS-Switches' Command Line Interface (CLI), Web UI, and REST interfaces, while also allowing managers to access other parts of the network, you should specify 192.168.1.0 255.255.255.0 as the authorized manager IP address on the switches. This configuration will restrict access to the switch management interfaces to devices within the specified IP address range, effectively creating a management access list.
| Page 7 out of 22 Pages |
| Previous |