
- Email support@dumps4free.com

According to the Risk Matrix table, what will be the risk level when the probability of an attack is very high, and the impact of that attack is major?
NOTE: It is mandatory to answer the question before proceeding to the next one.
A.
High
B.
Extreme
C.
Low
D.
Medium
High
Reference: https://onlinelibrary.wiley.com/page/journal/15396924/homepage/
special_issue
simple_characterisations_and_communication_of_risks.htm
Rinni, SOC analyst, while monitoring IDS logs detected events shown in the figure below.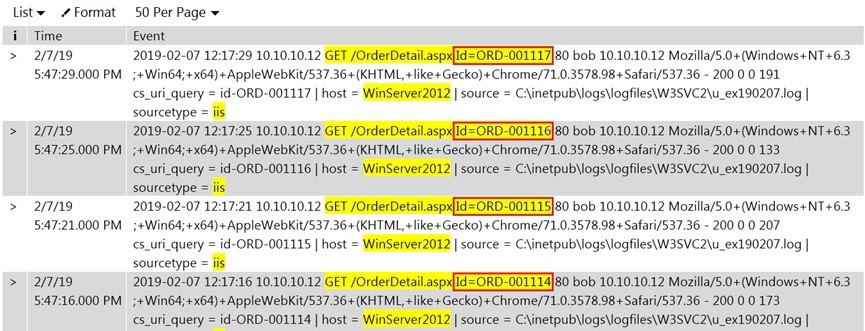
What does this event log indicate?
A.
Directory Traversal Attack
B.
XSS Attack
C.
SQL Injection Attack
D.
Parameter Tampering Attack
Parameter Tampering Attack
Reference: https://infosecwriteups.com/what-is-parameter-tampering-5b1beb12c5ba
The threat intelligence, which will help you, understand adversary intent and make
informed decision to ensure appropriate security in alignment with risk.
What kind of threat intelligence described above?
A.
Tactical Threat Intelligence
B.
Strategic Threat Intelligence
C.
Functional Threat Intelligence
D.
Operational Threat Intelligence
Strategic Threat Intelligence
Reference: https://www.blueliv.com/cyber-security-and-cyber-threat-intelligence-blogblueliv/
threat- intelligence/what-is-threat-intelligence/
An attacker exploits the logic validation mechanisms of an e-commerce website. He
successfully purchases a product worth $100 for $10 by modifying the URL exchanged
between the client and the server.
Original URL: http://www.buyonline.com/product.aspx?profile=12&debit=100 Modified URL:
http://www.buyonline.com/product.aspx?profile=12&debit=10
Identify the attack depicted in the above scenario.
A.
Denial-of-Service Attack
B.
SQL Injection Attack
C.
Parameter Tampering Attack
D.
Session Fixation Attack
Session Fixation Attack
An organization wants to implement a SIEM deployment architecture. However, they have the capability to do only log collection and the rest of the SIEM functions must be managed
by an MSSP. Which SIEM deployment architecture will the organization adopt?
A.
Cloud, MSSP Managed
B.
Self-hosted, Jointly Managed
C.
Self-hosted, MSSP Managed
D.
Self-hosted, Self-Managed
Self-hosted, MSSP Managed
| Page 6 out of 21 Pages |
| Previous |