
- Email support@dumps4free.com

Refer to the exhibit.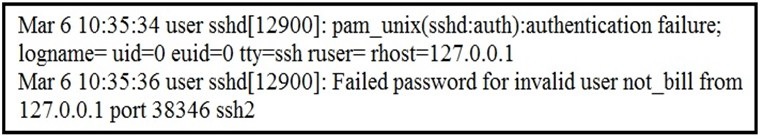
In which Linux log file is this output found?
A.
/var/log/authorization.log
B.
/var/log/dmesg
C.
var/log/var.log
D.
/var/log/auth.log
/var/log/auth.log
Which two components reduce the attack surface on an endpoint? (Choose two.)
A.
secure boot
B.
load balancing
C.
increased audit log levels
D.
restricting USB ports
E.
full packet captures at the endpoint
secure boot
restricting USB ports
An analyst is exploring the functionality of different operating systems.
What is a feature of Windows Management Instrumentation that must be considered when deciding on an operating system?
A.
queries Linux devices that have Microsoft Services for Linux installed
B.
deploys Windows Operating Systems in an automated fashion
C.
is an efficient tool for working with Active Directory
D.
has a Common Information Model, which describes installed hardware and software
has a Common Information Model, which describes installed hardware and software
An analyst is investigating an incident in a SOC environment.
Which method is used to identify a session from a group of logs?
A.
sequence numbers
B.
IP identifier
C.
5-tuple
D.
timestamps
5-tuple
What are two differences in how tampered and untampered disk images affect a security incident? (Choose two.)
A.
Untampered images are used in the security investigation process
B.
Tampered images are used in the security investigation process
C.
The image is tampered if the stored hash and the computed hash match
D.
Tampered images are used in the incident recovery process
E.
The image is untampered if the stored hash and the computed hash match
Tampered images are used in the security investigation process
The image is untampered if the stored hash and the computed hash match
| Page 5 out of 37 Pages |
| Previous |